Empowering Your Defense Strategy
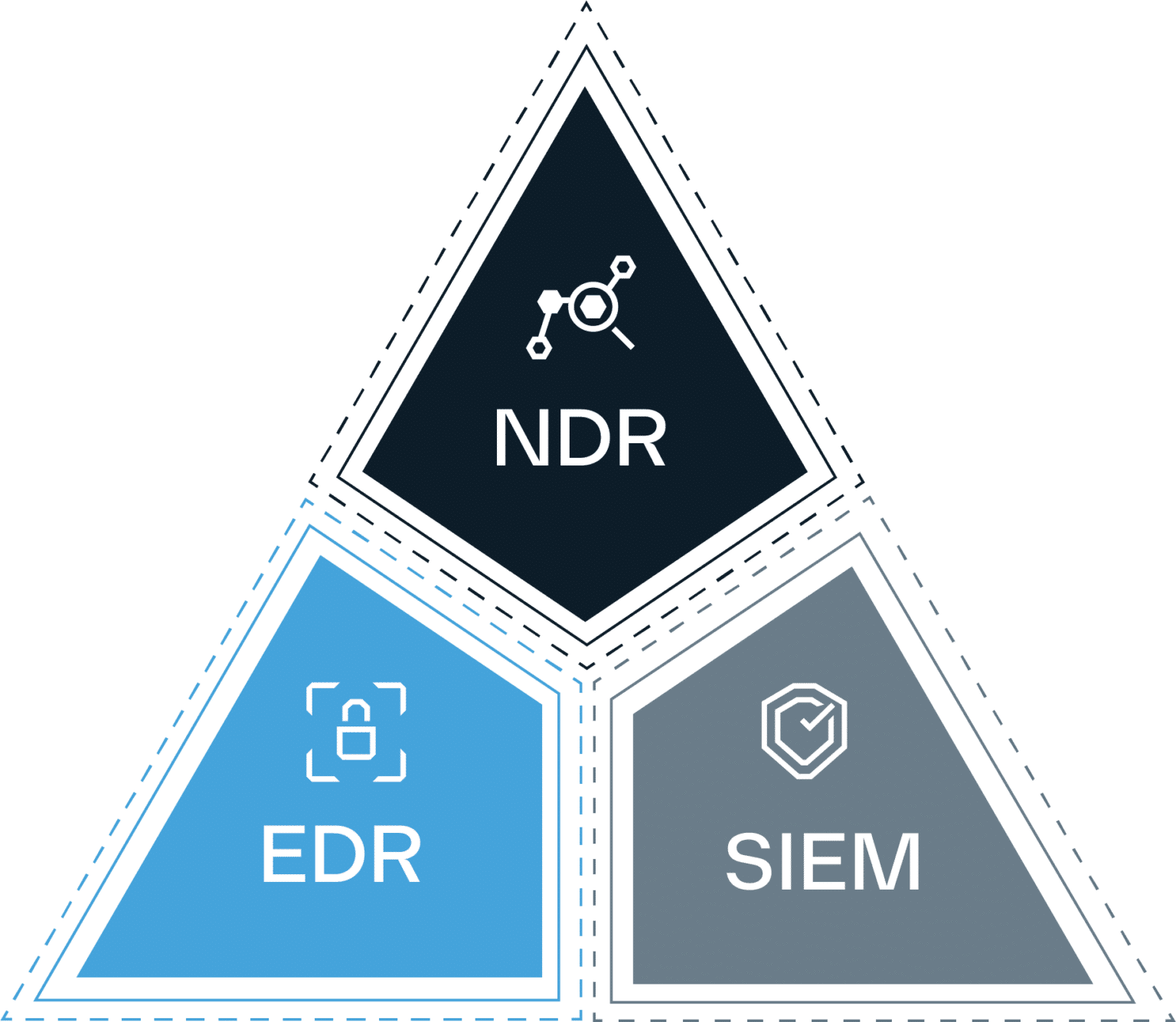
End Point Detection & Response (EDR)
Monitoring, detection, and recording of threats and suspicious activities or other problems on hosts or endpoints, used to ensure the health and safety of organizational digital assets.
Network Detection & Response (NDR)
Monitoring, detection, and recording of threats and suspicious activities or other problems on a given network and connected hosts, used to ensure the health and safety of organizational digital assets.
Security Incident & Event Management (SIEM)
Monitoring, detection, and recording of threats and suspicious activities or other problems within an IT environment using log retention and packet correlation rules, used to ensure the health and safety of organizational digital assets.
The numerous benefits from our white-glove MDR support services include, but are not limited to:
With more than 15 years of experience in Managed Detection and Response (MDR), Lumifi continues to improve customers’ security posture with our unique approach.
The management and oversight of an organization’s data assets to help provide business users with high-quality data that is easily accessible and consistent.
Forge a relationship that improves visibility and threat awareness, maximizes the potential of acquired technology, and matures security posture.
Unlike traditional MSSPs, Lumifi delivers service through a co-managed model, where your data is stored in your environment and accessed remotely by our team. We provide full management of the security tool, rather than joint management of the security tool.
Benefits: